- Cisco Anyconnect Free Download
- Cisco Anyconnect 3.1 Download Free
- Cisco Anyconnect 3.1 Eol
- Cisco Anyconnect 3.1 Download For Windows 10
- Cisco Anyconnect 3.1.13015
- Cisco Anyconnect 3.1.06
AnyConnect Pre-Deployment Package (Windows 10 ARM64) - includes individual MSI files Login and Service Contract Required anyconnect-win-arm64-4.10.00093-predeploy-k9.zip 08-Apr-2021. The remote host has a version of Cisco AnyConnect prior to 3.1(5187). It is, therefore, affected by an information disclosure vulnerability known as POODLE. The vulnerability is due to the way SSL 3.0 handles padding bytes when decrypting messages encrypted using block ciphers in.
Give any user highly secure access to the enterprise network, from any device, at any time, in any location.
Cisco AnyConnect - Empower your employees to work from anywhere, on company laptops or personal mobile devices, at any time. AnyConnect simplifies secure endpoint access and provides the security necessary to help keep your organization safe and protected.
Gain more insight into user and endpoint behavior with full visibility across the extended enterprise. With AnyConnect's Network Visibility Module (NVM), you can defend more effectively and improve network operations.
Defend against threats, no matter where they are. For example, with Cisco Identity Services Engine (ISE), you can prevent noncompliant devices from accessing the network. And with Cisco Umbrella Roaming, you can extend protection when users are off the VPN.
Provide a consistent user experience across devices, both on and off premises, without creating a headache for your IT teams. Simplify management with a single agent.
Cisco Anyconnect Free Download
Contents
Introduction
This document discusses the specific scenario where the AnyConnect client might reconnect to the Adaptive Security Appliance (ASA) in exactly one minute. The users might not be able to receive traffic over the Transport Layer Security (TLS) tunnel until AnyConnect reconnects. This is dependent upon a few other factors which are discussed in this document.
Affected Components
- ASA Release 9.0 or Release 9.1
- AnyConnect Client Release 3.0 or Release 3.1
Symptoms
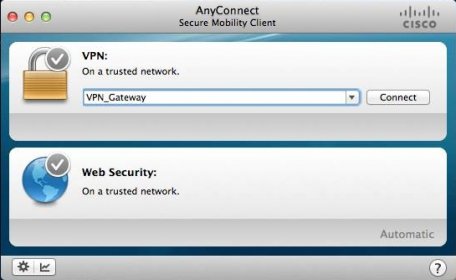
In this example, the AnyConnect client is shown as it reconnects to the ASA.
This syslog is seen on the ASA:
Problem Description
These Diagnostics and Reporting Tool (DART) logs are seen with this issue:
Causes
The cause of this issue is the failure to build a Datagram Transport Layer Security (DTLS) tunnel. This could be because of two reasons:
Cisco Anyconnect 3.1 Download Free
DTLS is blocked somewhere in the path
Use of a non-default DTLS port
DTLS is Blocked Somewhere in the Path

As of ASA Release 9.x and AnyConnect Release 3.x, an optimization has been introduced in the form of distinct Maximum Transition Units (MTUs) that are negotiated for TLS/DTLS between the client/ASA. Previously, the client derived a rough estimate MTU which covered both TLS/DTLS and was obviously less than optimal. Now, the ASA computes the encapsulation overhead for both TLS/DTLS and derives the MTU values accordingly.
As long as DTLS is enabled, the client applies the DTLS MTU (in this case 1418) on the VPN adapter (which is enabled before the DTLS tunnel is established and is needed for routes/filters enforcement), to ensure optimum performance. If the DTLS tunnel cannot be established or it is dropped at some point, the client fails over to TLS and adjusts the MTU on the virtual adapter (VA) to the TLS MTU value (this requires a session level reconnect).

Cisco Anyconnect 3.1 Eol
Resolution
In order to eliminate this visible transition of DTLS > TLS, the administrator can configure a separate tunnel group for TLS only access for users that have trouble with the establishment of the DTLS tunnel (such as due to firewall restrictions).
The best option is to set the AnyConnect MTU value to be lower than the TLS MTU, which is then negotiated.
This makes TLS and DTLS MTU values equal. Reconnections are not seen in this case.
The second option is to allow fragmentation.
With fragmentation, large packets (whose size exceeds the MTU value) can be fragmented and sent through the TLS tunnel.
The third option is to set the Maximum Segment Size (MSS) to 1460 as follows:
In this case, the TLS MTU will be 1427 (RC4/SHA1) which is larger than the DTLS MTU 1418 (AES/SHA1/LZS). This should resolve the issue with TCP from the ASA to the AnyConnect client (thanks to MSS), but large UDP traffic from the ASA to the AnyConnect client might suffer from this as it will be dropped by the AnyConnect client due to the lower AnyConnect client MTU 1418. If sysopt conn tcpmss is modified, it might affect other features such as LAN-to-LAN (L2L) IPSec VPN tunnels.
Use of a Non-default DTLS Port
Cisco Anyconnect 3.1 Download For Windows 10
Another potential cause for the DTLS failure is enabling DTLS on a non-default port after the WebVPN is enabled (for example, when the webvpn enable outside command is entered). This is due to Cisco bug ID CSCuh61321 and has been seen in Release 9.x where the ASA pushes the non-default port to the client, but continues to listen to the default port. Consequently, the DTLS is not built and AnyConnect reconnects.
After the TLS tunnel is established, the client attempts to establish the DTLS tunnel to port 444 as expected :
The order of the commands that lead to the problem and the accelerated security path (ASP) table sockets opened is:
Start with the WebVPN sockets not enabled.
Change TLS port to 444 and enable WebVPN.
Change the DTLS port to 444.
Note: The DTLS socket port is still 443. At this point the AnyConnect clients establish DTLS to 444 though!
Resolution
The workaround for this problem is to follow the order of :
Disable the WebVPN.
Enter the DTLS port.
Enable the WebVPN.
This behaviour does not exist in Release 8.4.x versions, where the DTLS sockets get updated with the configured ports immediately after the configuration is entered:
ASA Release 8.4.6 :
Reconnect Workflow
Suppose that these ciphers are configured:
This sequence of events takes place in this case:
- AnyConnect establishes a parent tunnel and a TLS data tunnel with RC4-SHA as the SSL encryption.
- DTLS is blocked in the path and a DTLS tunnel cannot be established.
- ASA announces parameters to AnyConnect, which includes TLS and DTLS MTU values, which are two separate values.
- DTLS MTU is 1418 by default.
- TLS MTU is calculated from the sysopt conn tcpmss value (default is 1380). This is how the TLS MTU is derived (as seen from the debug webvpn anyconnect output):
- AnyConnect brings the VPN adapter up and assigns DTLS MTU to it in anticipation that it will be able to connect via DTLS.
- The AnyConnect client is now connected and the user goes to a particular website.
- The browser sends TCP SYN and sets MSS = 1418-40 = 1378 in it.
- The HTTP-server on the inside of the ASA sends packets of size 1418.
- The ASA cannot put them into the tunnel and cannot fragment them as they have Don't Fragment (DF) bit set.
- ASA printsand drops packets with mp-svc-no-fragment-ASP drop reason.
- At the same time the ASA sends ICMP Destination Unreachable, Fragmentation Needed to the sender:
- If Internet Control Message Protocol (ICMP) is allowed, then the sender retransmits dropped packets and everything starts to work. If ICMP is blocked, then traffic is blackholed on the ASA.
- After several retransmits it understands that the DTLS tunnel cannot be established and it needs to reassign a new MTU value to the VPN adapter.
- The purpose of this reconnect is to assign a new MTU.
For more information on reconnect behavior and timers, see AnyConnect FAQ: Tunnels, Reconnect Behavior, and the Inactivity Timer
Caveats
Cisco Anyconnect 3.1.13015
Cisco bug ID CSCuh61321 AC 3.1:ASA incorrectly handles alternate DTLS port,causes reconnect
Cisco Anyconnect 3.1.06
Related Information
